In a digital landscape that’s more mobile-reliant than ever, the small devices in our pockets have become hubs of communication, storage, finance, and even identification. As a result, mobile security has become a critical aspect of personal and organizational safety. With a rise in the sophistication and variety of mobile threats—including more believable phishing scams, mobile-specific malware, and the dangers of public networks—it’s imperative to know your way around common vulnerabilities.
Modern mobile security threats cut across demographics, impacting individuals and entities regardless of technical literacy. They underscore the necessity to treat mobile security with the same gravity given to traditional cybersecurity. This blog post explores the top mobile security threats you should know about and gives you key tips, practices, and solutions for fortifying your own devices and network against them.
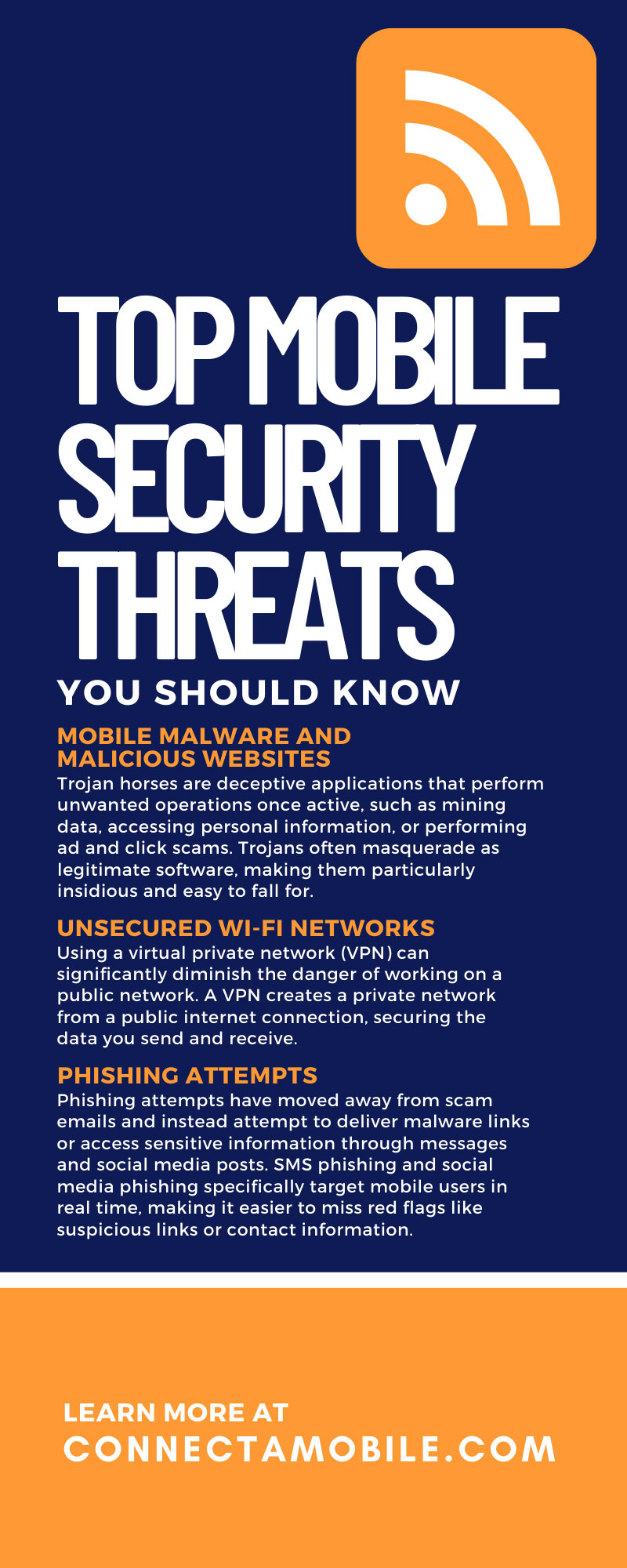
Mobile Malware and Malicious Websites
Malicious software, or malware, presents a multifaceted threat to mobile users. From siphoning data to causing system failures, malware is not just a nuisance but a significant risk. Malware is not a new type of security threat, but it is continuously evolving to specifically target mobile devices. There are many forms of malware, but the most common malicious mobile apps that pose a risk are ransomware and trojans.
Mobile ransomware encrypts a victim’s files and demands a ransom in exchange for the decryption key. Ransomware cuts off data access and can completely halt communications on your device.
Trojan horses are deceptive applications that perform unwanted operations once active, such as mining data, accessing personal information, or performing ad and click scams. Trojans often masquerade as legitimate software, making them particularly insidious and easy to fall for.
Vigilance is paramount to protect your mobile device against malware. Paying close attention to what you download and setting strict application permissions is critical. You can also help secure your device through safeguard applications that ensure privacy and security when communicating and browsing on your phone.
Unsecured Wi-Fi Networks
Public Wi-Fi networks are convenient yet fraught with risk. Hackers often exploit vulnerabilities in these networks to gain access to user data. Some attackers will even set up a fraudulent network specifically to access and attack any devices that connect to it.
Using a virtual private network (VPN) can significantly diminish the danger of working on a public network. A VPN creates a private network from a public internet connection, securing the data you send and receive.
Phishing Attempts
Phishing is a deceitful attempt to acquire sensitive information by posing as a trustworthy entity. This is one of the most common mobile security threats to know about. Chances are, you’ve seen poorly designed emails requesting personal data like passwords or bank information for obvious scams. However, as cybersecurity evolves, so do phishing attempts; they’re more sophisticated and believable than ever before.
When it comes to mobile devices, phishing attempts have moved away from scam emails and instead attempt to deliver malware links or access sensitive information through messages and social media posts. SMS phishing and social media phishing specifically target mobile users in real time, making it easier to miss red flags like suspicious links or contact information.
In the never-ending arms race with phishers, suspicion is your best weapon. Scrutinizing messages, avoiding clicking on links from unknown sources, and always verifying the authenticity of requests can help evade most phishing hooks.
Man-in-the-Middle (MitM) Attacks
Man-in-the-middle attacks occur when a third party intercepts, steals, or modifies communications between two parties. Mobile users are particularly at risk for these kinds of attacks because of the relative ease of intercepting SMS messages or unencrypted mobile browsing. Additionally, with increased reliance on mobile banking, shopping, and other sensitive communications, MitM attacks have grown in scale and potential impact on mobile users.
MitM attacks are common on public Wi-Fi and cellular networks, which are more vulnerable to cyberattacks and increase your risk of insecure communication. Limiting the use of unsecured networks, utilizing strong encryption, and verifying the security of the websites you visit can keep potential attackers at bay.
Jailbreaking and Rooting
Jailbreaking or rooting a mobile device involves attackers exploiting vulnerabilities in a phone’s operating system to hack the device and gain administrative access. From there, hackers can alter permissions and settings to gain access to more data and cause more harm to the device and its owner. Jailbreaking and rooting make mobile devices more susceptible to a host of security issues. These attacks can exacerbate the damage of other mobile security breaches, including malware, insecure communications, and more.
Internet of Things (IoT) Devices
In a world where connectivity is king, the rise of IoT devices has been meteoric. The IoT has revolutionized convenience, allowing for the remote management of home systems, health monitoring, and much more. An Internet of Things network extends far beyond computers and smartphones to encompass everyday objects, including wearable tech like smartwatches and crucial equipment like smart appliances.
However, this expanded connectivity also offers an array of vulnerabilities that attackers can exploit. Unsecured IoT devices are akin to open doors, providing a direct conduit to an individual’s network and, by extension, their most sensitive data.
Lost or Stolen Devices
The disappearance of a mobile device, whether through theft or simple misplacement, can become a harrowing ordeal laced with security implications. The sensitive nature of the data on these devices makes them a particularly potent target for malicious actors.
The most immediate danger that arises from a lost or stolen mobile device is the potential breach of personal information. This can result in identity theft, unauthorized financial transactions, and the unearthing of private correspondence that can be leveraged in various malicious schemes.
Even with extreme vigilance and care, theft or loss are common dangers for mobile phone users. That’s why it’s important to utilize advancements in mobile technology, such as remote device management. This solution allows users to locate, lock, and even erase their device’s data from afar. These tools provide a line of defense against the threats that come with device loss.
Protect Your Phone With Connecta Mobile
Mobile security threats are constantly evolving, but they don’t have to define the way you use your device. By choosing a secure mobile network for your device, you can guarantee both convenience and privacy whenever you talk, text, or browse. Enjoy high-speed connectivity and dependable privacy and confidentiality when you purchase a secure cell phone and plan from Connecta Mobile today.